ISO 27001 requirements information security management systems version 2022
16/02/2025
Quiz requirements ISO 27001 version 2022 You want to familiarize yourself with the structure of the standard, identify and understand the requirements of ISO 27001 version 2022, then it's up to you to play!
The quiz "ISO 27001 Requirements version 2022" will help you understand the main requirements of the standard.
The questions (requirements) for this quiz are 79, don't panic. The requirements of the standard are 236 but these 79 requirements are among the most important, so don't hesitate to learn in a fun way!
Don't think that you can complete this quiz in less than an hour, or even two hours, unless of course you are a little genius!
News on the information security standard ISO 27001 version 2022
The 236 requirements (shall, shall) of clauses 4 to 10 and annex A of ISO 27001 are broken down as follows:
|
No
|
Clause
|
PDCA cycle
|
Requirement No
|
Quantity
|
|
4
|
Context | Plan |
1 ÷ 11
|
11
|
| 5 | Leadership | Plan, Do, Check, Act |
12 ÷ 29
|
18 |
| 6 | Planning | Plan |
30 ÷ 68
|
39
|
| 7 | Support | Do |
69 ÷ 92
|
24 |
| 8 | Operation | Do |
93 ÷ 101
|
9 |
| 9 | Performance | Check | 102 ÷ 131 | 30 |
| 10 | Improvement | Act | 132 ÷ 143 | 12 |
| Annex A | Plan, Do, Check, Act | 144 ÷ 236 | 93 | |
|
Total
|
236
|
|||
(1).jpg)
Requirements in ISO 27001 clauses, sub-clauses and annex A
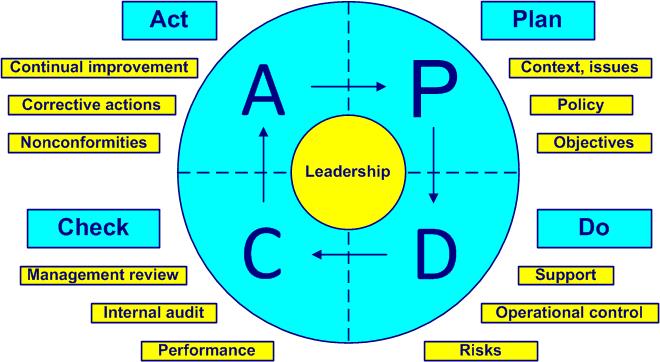
Deming PDCA cycle
Note. Any requirement normally begins with "The organization shall ...". For simplicity we present the requirements directly starting with the verb.
|
ISO 27001 - Requirements and comments version 2022
|
||||
|
No
|
Clause
(sub-clause)
|
Requirement
|
PDCA cycle, links, comments
|
|
|
Context
|
||||
|
4.1
|
The organization and its context
|
|||
|
1
|
4.1
|
Determine external and internal issues | Understand everything that can influence the purpose (mission) of the company (corporate culture, innovation, strategic orientation, competition, market, obligations, working time, working conditions) and its ability to obtain the expected results of the ISMS. See sub-clauses 6.1 and 7.5.1 | |
|
2
|
4.1
|
Determine whether climate change is a relevant issue | Amendment 1 to ISO 27001: 2020: Climate action changes | |
|
4.2
|
Stakeholders
|
|
||
|
3
|
4.2 a
|
Determine stakeholders | Concerned with the ISMS, such as laws, contracts and others. See sub-clause 7.5.1 | |
| 4 | 4.2 b | Determine needs and expectations | Of the stakeholders relating to information security requirements and obligations | |
| 5 | 4.2 c | Determine requirements concerned by the ISMS | Requirements addressed by the ISMS | |
|
4.3
|
Scope
|
|||
|
6
|
4.3
|
Determine the scope of the ISMS | (Administrative) limits and applicability | |
| 7 | 4.3 a | Take into account external and internal issues | "To determine hazards is to reduce risks". Cf. sub-clause 4.1 | |
| 8 | 4.3 b | Take into account the requirements of the stakeholders | When changing processes, requirements, infrastructure. See sub-clause 4.2 | |
| 9 | 4.3 c | Take into account the professional interfaces | "No-risk situations do not exist". Interactivity of internal activities and those of other organizations | |
| 10 | 4.3 | Make the scope available as a document | Cf. sub-clause 7.5.1 | |
|
4.4
|
Information security management system
|
|
||
| 11 | 4.4 | Establish, implement and maintain and improve the ISMS | "If you cannot describe what you are doing as a process, you do not know what you're doing". Edwards Deming. In accordance with the requirements of ISO 27001. Information security manual, cf. sub-clause 7.5.1 | |
|
5
|
Leadership
|
|||
|
5.1
|
Leadership and commitment
|
|||
| 12 | 5.1 a | Ensure that the information security policy and objectives are established |
"When you sweep the stairs, you start at the top. Romanian proverb." Ensure compatibility with strategic direction. Top management is showing leadership. Affirm top management's commitment to the ISMS |
|
| 13 | 5.1 b | Ensure that ISMS requirements are integrated into business processes | Show leadership | |
| 14 | 5.1 c | Ensure that the necessary resources for the ISMS are available | Resources to establish, apply, maintain and improve the ISMS. Cf. sub-clause 4.4 | |
| 15 | 5.1 d | Communicate on the importance of an effective ISMS | And comply with the requirements of ISO 27001 | |
| 16 | 5.1 e | Ensure that the ISMS achieves the intended results | Commitment, responsiveness and active support from top management | |
| 17 | 5.1 f |
Guide and support people |
In order to contribute to the performance of the ISMS | |
| 18 | 5.1 g | Promote continual improvement | "Employees first, customers second. Vineet Nayar." Show leadership. Cf. clause 10 | |
| 19 | 5.1 h | Help those affected to show leadership | When necessary for their area of responsibility | |
|
5.2
|
Policy
|
|
||
| 20 | 5.2 a | Establish an information security policy | Taking into account the mission of the organization. Keep the policy up to date. Cf. sub-clause 7.5.1 | |
| 21 | 5.2 b | Provide a framework for establishing information security objectives | Cf. sub-clause 6.2 | |
| 22 | 5.2 c | Commit to meet applicable requirements | Regarding information security | |
| 23 | 5.2 d | Commit to continual improvement of the ISMS | Cf. clause 10 | |
| 24 | 5.2 e | Make the information security policy available as a document | Cf. sub-clause 7.5.1 | |
| 25 | 5.2 f | Communicate the information security policy | At all levels of the organization | |
| 26 | 5.2 g | Keep the information security policy available to stakeholders | If applicable | |
|
5.3
|
Roles, responsibilities and authorities
|
|
||
| 27 | 5.3 | Ensure that responsibilities and authorities for the ISMS are assigned | And communicated at all levels of the organization. "Responsibility cannot be shared. Robert Heinlein". Cf. sub-clause 7.5.1 | |
| 28 | 5.3 a | Ensure that the ISMS meets the requirements of the ISO 27001 standard | And who has the responsibility and authority at all levels of the organization. Remember that in the end top management is fully responsible (cf. sub-clause 5.1) | |
| 29 | 5.3 b | Submit reports on ISMS performance to top management on a regular basis | By assigning responsibility and authority by name, cf. sub-clause 7.5.1 | |
|
6
|
Planning
|
|||
|
6.1
|
Actions to address risks
|
|||
|
6.1.1
|
General
|
|
||
| 30 | 6.1.1 a | Determine risks and opportunities | In order to ensure that the ISMS can achieve the expected results. Cf. sub-clause 4.1 for issues and sub-clause 4.2 for requirements. An inventory of the situation is always useful before planning. "Any decision involves a risk. Peter Barge" | |
| 31 | 6.1.1 b | Determine risks and opportunities | In order to anticipate or reduce side effects | |
| 32 | 6.1.1 c | Determine risks and opportunities | In order to be part of the continual improvement process, cf. clause 10 | |
| 33 | 6.1.1 d | Plan actions to address these risks and opportunities | Cf. sub-clause 6.1.3 | |
| 34 | 6.1.1 e 1 | Plan how to integrate and implement the necessary actions | For all processes of the ISMS | |
| 35 | 6.1.1 e 2 | Plan how to assess the effectiveness of actions taken | Cf. sub-clause 6.1.3 | |
|
6.1.2
|
Risk assessment
|
|||
| 36 | 6.1.2 a 1 | Apply an information security risk assessment process | By establishing and maintaining acceptance criteria | |
| 37 | 6.1.2 a 2 | Apply an information security risk assessment process | By establishing and updating the criteria for carrying out assessments | |
| 38 | 6.1.2 b | Apply an information security risk assessment process | By ensuring that the repetition of risk assessments leads to consistent, valid and comparable results. Impossible physical and intellectual challenge. Cf. the Oxebridge blog :"iso-risk-management-can-now-be-infallible" | |
| 39 | 6.1.2 c 1 | Apply an information security risk assessment process | By identifying the risks associated with the loss of confidentiality, integrity and availability of information | |
| 40 | 6.1.2 c 2 | Apply an information security risk assessment process | By identifying the risk owners | |
| 41 | 6.1.2 d 1 | Apply an information security risk assessment process |
By analyzing the risks and the potential consequences of risks in 6.1.2 c 1 materializing |
|
| 42 | 6.1.2 d 2 | Apply an information security risk assessment process | By analyzing the risks and assessing the likelihood of occurrence of the risks identified in 6.1.2 c 1 | |
| 43 | 6.1.2 d 3 | Apply an information security risk assessment process | By analyzing risks and determining risk levels | |
| 44 | 6.1.2 e 1 | Apply an information security risk assessment process | By evaluating the risks and comparing the results of the risk analysis with the criteria in 6.1.2 a | |
| 45 | 6.1.2 e 2 | Apply an information security risk assessment process | By evaluating the risks and prioritizing the analyzed risks | |
| 46 | 6.1.2 | Retain a record on the information security risk assessment process | Cf. sub-clause 7.5.1 | |
|
6.1.3
|
Risk treatment
|
|||
| 47 | 6.1.3 a | Apply an information security risk treatment process | In order to choose the risk treatment options taking into account the results in 6.1.2 | |
| 48 | 6.1.3 b | Apply an information security risk treatment process | In order to determine the necessary measures to be taken for the chosen option | |
| 49 | 6.1.3 c | Apply an information security risk treatment process | In order to compare the measurements determined in 6.1.3 b and those of annex A of ISO 27001 | |
| 50 | 6.1.3 d | Apply an information security risk treatment process | In order to produce a statement of applicability including the necessary measures (cf. 6.1.3 b and c), the justification for their inclusion, their implementation (or not), the justification for the exclusion of controls from Annex A of ISO 27001 | |
| 51 | 6.1.3 e | Apply an information security risk treatment process | In order to develop a risk treatment plan, cf. sub-clause 6.2 | |
| 52 | 6.1.3 f | Apply an information security risk treatment process | In order to obtain from the risk owners the validation of the risk treatment plan and the acceptance of residual risks | |
| 53 | 6.1.3 | Retain a record on the information security risk treatment process | Cf. sub-clause 7.5.1 | |
|
6.2
|
Objectives
|
|||
| 54 | 6.2 | Establish information security objectives | For all functions and levels in the organization | |
| 55 | 6.2 a | Determine information security objectives | Consistent with the organization's information security policy | |
| 56 | 6.2 b | Determine information security objectives | Measurable, if possible | |
| 57 | 6.2 c | Determine information security objectives | Taking into account the requirements applicable to information security, the results of the risk assessment and treatment | |
| 58 | 6.2 d | Determine information security objectives | And monitor them, cf. sub-clause 9.1 | |
| 59 | 6.2 e | Determine information security objectives | And communicate them, cf. sub-clause 7.4 | |
| 60 | 6.2 f | Determine information security objectives | And update them, if appropriate | |
| 61 | 6.2 g | Determine information security objectives | And retain them as documents, cf. sub-clause 7.5 | |
| 62 | 6.2 | Retain a record on objectives | Related to information security, including the objective achievement plan, cf. sub-clause 7.5.1 | |
| 63 | 6.2 h | Determine when planning information security objectives | What will be done | |
| 64 | 6.2 i | Determine when planning information security objectives | The necessary resources | |
| 65 | 6.2 j | Determine when planning information security objectives | The responsible | |
| 66 | 6.2 k | Determine when planning information security objectives | The deadlines | |
| 67 | 6.2 l | Determine when planning information security objectives | How the results will be evaluated | |
|
Planning of changes
|
|
|||
| 68 | 6.3 | Plan the changes of the ISMS | Before applying them | |
|
7
|
Support
|
|||
|
7.1
|
Resources
|
|||
|
69
|
7.1
|
Identify and provide the resources needed | In order to establish, apply, maintain and improve the ISMS | |
|
7.2
|
Competence
|
|
||
| 70 | 7.2 a | Determine the necessary competence of the people involved | Those involved can affect information security performance | |
| 71 | 7.2 b | Ensure that these people are competent | On the basis of initial and professional training and experience | |
| 72 | 7.2 c | Take actions to acquire and keep the necessary competence updated | And evaluate the effectiveness of these actions. Actions include training, but also supervision, reassignment and recruitment of competent people | |
| 73 | 7.2 d | Retain a record on competence | Cf. sub-clause 7.5.1 like the competence development plan | |
|
7.3
|
Awareness
|
|
||
|
74
|
7.3 a
|
Make people aware of the information security policy and objectives | Cf. sub-clauses 5.2 and 6.2. Awareness enhancement plan, cf. sub-clause 7.5.1 | |
| 75 | 7.3 b | Make people aware of the importance of their contribution to the effectiveness of the ISMS | And the beneficial effects of improved performance of the ISMS | |
| 76 | 7.3 c | Make people aware of the repercussions and consequences of not conforming with ISMS requirements | Do not forget the potential consequences on all professional activities | |
|
7.4
|
Communication
|
|||
| 77 | 7.4 a | Determine internal and external communication needs | Including on which subjects, communication improvement plan, cf. sub-clause 7.5.1 | |
| 78 | 7.4 b | Determine internal and external communication needs | Including when | |
| 79 | 7.4 c | Determine internal and external communication needs | Including with whom | |
| 80 | 7.4 d | Determine internal and external communication needs | Including who shall communicate | |
|
7.5
|
Documentation
|
|||
|
7.5.1
|
General
|
|
||
| 81 | 7.5.1 a | Include in the ISMS the documentation required by ISO 27001 |
Procedures (documented information to maintain):
Policies:
Records (documented information to retain):
|
|
| 82 | 7.5.1 b | Include documentation deemed necessary for the effectiveness of the ISMS |
This documentation is specific in relation to the size of the organization, to the field of activity, to the complexity of the processes and their interactions to the competence of the personnel |
|
|
7.5.2
|
Creating and updating
|
|||
| 83 | 7.5.2 a | Identify and describe the documentation appropriately | When creating and updating. As title, author, date, codification | |
| 84 | 7.5.2 b | Ensure that the format and media of the documentation is appropriate | Examples of formats: language, software version and graphics. Examples of media: paper, electronic | |
| 85 | 7.5.2 c | Review and validate documentation appropriately | In order to determine their relevance and suitability | |
|
7.5.3
|
Document control
|
|||
| 86 | 7.5.3 a | Control documentation so that it is available and suitable for use | When and where needed. According to the requirements of the ISMS and the ISO 27001 standard | |
| 87 | 7.5.3 b | Control documentation so that it is properly protected | As loss of confidentiality, improper use or loss of integrity | |
| 88 | 7.5.3 c | Apply distribution, access, retrieval and usage activities | In order to control the documentation | |
| 89 | 7.5.3 d | Apply storage and preservation activities | Including legibility preservation | |
| 90 | 7.5.3 e | Apply change control activities | Like version control | |
| 91 | 7.5.3 f | Apply retention and disposition activities | By determining for each document the retention period and the way of disposal | |
| 92 | 7.5.3 | Identify and control documents of external origin | List of documentation deemed necessary for the planning and operation of the ISMS, including that of external origin. Cf. sub-clause 7.5.1 | |
|
8
|
Operation
|
Do | ||
|
8.1
|
Planning and control
|
|||
| 93 |
8.1 | Plan, apply, control and maintain the processes necessary to meet the requirements of the ISMS | By establishing criteria for these processes and carrying out specific actions in the sub-clause 6.1 | |
| 94 | 8.1 | Plan, apply, control and maintain the processes necessary to meet the requirements of the ISMS | By applying the control in accordance with the criteria | |
| 95 | 8.1 | Retain documentation on the necessary processes | In order to ensure that the processes are carried out as planned. Cf. sub-clause 7.5.1 | |
| 96 | 8.1 | Control planned changes and analyze unforeseen changes | By taking actions to limit any negative impact. Cf. sub-clause 7.5.1 | |
| 97 | 8.1 | Ensure that outsourced processes are controlled and relevant | Including outsourced products and services | |
|
Risk assessment
|
|
|||
| 98 | 8.2 | Assess information security risks regularly | Taking into account the criteria established in 6.1.2 a and sub-clause 6.3 | |
| 99 | 8.2 | Retain a record on the results of the risk assessment | Results of risk assessment, cf. sub-clause 7.5.1 | |
|
Risk treatment
|
|
|||
| 100 | 8.3 | Apply the risk treatment plan | In accordance with sub-clause 6.2 | |
| 101 | 8.3 | Retain a record on the results of the risk treatment | Risk treatment plan, cf. sub-clause 7.5.1 | |
|
9
|
Performance
|
|||
|
Inspection
|
||||
| 102 | 9.1 a | Determine what to inspect (monitor and measure) | Including information security processes and measures | |
| 103 | 9.1 b | Determine inspection methods | Including analysis and evaluation to ensure the validity of the results. Any valid result is comparable and reproducible | |
| 104 | 9.1 c | Determine when to inspect | Including the points where monitoring and measurement are carried out | |
| 105 | 9.1 d | Determine who performs the inspection | The person responsible for the inspection | |
| 106 | 9.1 e | Determine when to analyze inspection results | Including the moment of evaluation of the results | |
| 107 | 9.1 f | Determine who analyzes the results | Including the person responsible for evaluating the results | |
| 108 | 9.1 | Retain a record on inspection results | Cf. sub-clause 7.5.1 | |
| 109 | 9.1 | Evaluate the information security performance | Including the effectiveness of the ISMS | |
|
Internal audit
|
||||
|
9.2.1
|
General
|
|
||
| 110 | 9.2.1 a 1 | Perform internal audits at scheduled intervals to provide information to determine whether the ISMS meets organizational requirements | Including policy and objectives, cf. sub-clauses 5.2 and 6.2 | |
| 111 | 9.2.1 a 2 | Perform internal audits at scheduled intervals to provide information to determine whether the ISMS meets ISO 27001 requirements | Requirements in clauses 4 to 10 of the standard | |
| 112 | 9.2.1 b | Perform internal audits at scheduled intervals to provide information to determine whether the ISMS meets ISO 27001 requirements | Cf. management review, sub-clause 9.3 | |
|
9.2.2
|
Internal audit program
|
|
||
| 113 | 9.2.2 | Plan, establish, apply and maintain the audit program | Including frequency, methods, responsibilities, planning and reporting requirements. Follow the recommendations of ISO 19011 | |
| 114 | 9.2.2 | Take into account in the audit program the importance of the processes | And results of previous audits | |
| 115 | 9.2.2 a | Define the audit criteria | And the scope of each audit. Follow the recommendations of ISO 19011 | |
| 116 | 9.2.2 b | Select auditors | In order to carry out objective and impartial audits. Follow the recommendations of ISO 19011 | |
| 117 | 9.2.2 c | Report the results of the audits | To the direction concerned | |
| 118 | 9.2.2 | Retain a record on the application of the audit program | And audit results, cf. sub-clause 7.5.1 | |
|
Management review
|
||||
|
9.3.1
|
General
|
|
||
| 119 | 9.3.1 | Review the ISMS at scheduled intervals | To ensure that the ISMS is still appropriate, adequate and effective. "No system is perfect" | |
|
9.3.2
|
Management review inputs
|
|
||
| 120 | 9.3.2 a | Take into consideration the progress of actions decided during the previous management review | Use the latest management review report | |
| 121 | 9.3.2 b | Take into consideration the modifications of the relevant issues for the ISMS | Cf. sub-clause 4.1 | |
| 122 | 9.3.2 c | Consider changing stakeholders' requirements | Cf. sub-clause 4.2 | |
| 123 | 9.3.2 d 1 | Consider feedback trends |
Including nonconformities and corrective actions, cf. sub-clause 10.2 |
|
| 124 | 9.3.2 d 2 | Consider trends in inspection results | In other words, the results of monitoring and measurement, cf. sub-clause 9.1 | |
| 125 | 9.3.2 d 3 | Consider trends in audit results |
Cf. sub-clause 9.2 |
|
| 126 | 9.3.2 d 4 | Take into consideration the trends of objective achievement | Cf. sub-clause 6.2 | |
| 127 | 9.3.2 e | Consider feedback from stakeholders |
Cf. sub-clause 4.2 |
|
| 128 | 9.3.2 f | Consider the results of the risk assessment | Including the progress of the risk treatment plan, cf. paragraph 6.1.3 | |
| 129 | 9.3.2 g | Consider opportunities for continual improvement | And any changes to the ISMS, cf. sub-clause 10.2 | |
|
9.3.3
|
Management review results
|
|
||
| 130 | 9.3.3 | Include continuous improvement decisions in the results of the management review | And any changes to the ISMS, cf. sub-clause 10.2 | |
| 131 | 9.3.3 | Retain a record on the conclusions of the management review | Cf. sub-clause 7.5.1 | |
|
10
|
Improvement
|
|||
|
10.1
|
Continual improvement
|
|||
| 132 | 10.1 |
Continually improve the suitability, adequacy and effectiveness of the ISMS
|
By improving overall performance | |
|
Nonconformity and corrective action
|
|
|||
| 133 | 10.2 a 1 | React to the nonconformity | In order to control and correct it | |
| 134 | 10.2 a 2 |
React to the nonconformity |
In order to deal with the consequences of nonconformity | |
| 135 | 10.2 b 1 |
Review the nonconformity |
Evaluate whether action is needed to eliminate the cause | |
| 136 | 10.2 b 2 | Find the cause of the nonconformity | If possible the root cause | |
| 137 | 10.2 b 3 | Find out if similar nonconformities have occurred | Or could occur | |
| 138 | 10.2 c | Implement any action needed | Including corrective actions | |
| 139 | 10.2 d | Review the effectiveness of any undertaken action | Including any corrective action | |
| 140 | 10.2 e | Make changes to the ISMS | If necessary | |
| 141 | 10.2 | Take corrective actions appropriate to actual or potential consequences | In relation to the nonconformities that appeared | |
| 142 | 10.2 f | Retain a record on the nature of nonconformities | Cf. sub-clause 7.5.1 | |
| 143 | 10.2 g | Retain a record on the results of corrective actions | Cf. sub-clause 7.5.1 | |
|
Annex A (normative)
|
|
|||
|
A.5 Organizational controls
|
||||
| 144 | A.5.1 | Policies for information security | Define information security policies, which are approved by top management, published, communicated, reviewed and changed, cf. sub-clause 5.2 | |
| 145 | A.5.2 | Information security roles and responsibilities | Define and assign functions and responsibilities related to information security, cf. sub-clause 5.3 | |
| 146 | A.5.3 | Segregation of duties | Segregate conflicting duties and areas of responsibilities | |
| 147 | A.5.4 | Management responsibilities | Apply information security measures according to company policies and procedures, as requested by top management, cf. sub-clause 5.1 | |
| 148 | A.5.5 | Contact with authorities | Establish and maintain contact with relevant authorities | |
| 149 | A.5.6 | Contact with special interest groups | Establish and maintain contacts with interest groups related to information security | |
| 150 | A.5.7 | Threat intelligence | Collect and analyze information security threats | |
| 151 | A.5.8 | Information security in project management | Integrate information security into project management | |
| 152 | A.5.9 | Inventory of information and other associated assets | Develop and maintain an inventory of information and assets related to information security | |
| 153 | A.5.10 | Acceptable use of information and other associated assets | Identify, document and apply rules for acceptable use and procedures for handling information and assets | |
| 154 | A.5.11 | Return of assets | Return all assets upon leaving the company or changing employment contract | |
| 155 | A.5.12 | Classification of information | Classify information according to confidentiality, integrity and availability requirements | |
| 156 | A.5.13 | Labeling of information | Develop and implement procedures for information labeling | |
| 157 | A.5.14 | Information transfer | Establish rules, procedures or agreements on the transfer of information internally and with stakeholders | |
| 158 | A.5.15 | Access control | Define and apply rules for physical and logical access to information according to business requirements and information security | |
| 159 | A.5.16 | Identity management | Manage the full life cycle of identities | |
| 160 | A.5.17 | Authentication information | Control the allocation and management of authentication information according to a specific process including recommendations for appropriate use | |
| 161 | A.5.18 | Access rights | Provide, review, modify and remove access rights to information and assets in accordance with the topic-specific policy | |
| 162 | A.5.19 | Information security in supplier relationships | Define and apply processes and procedures to manage information security risks associated with the use of supplier's products and services | |
| 163 | A.5.20 | Addressing information security within supplier agreements | Set up and agree with each supplier the appropriate information security requirements | |
| 164 | A.5.21 | Managing information security in the information and communication technology (ICT) supply chain | Define and apply processes and procedures to manage information security risks related to the ICT products and services supply chain | |
| 165 | A.5.22 | Monitoring review and change management of supplier services | Regularly monitor, review, evaluate and manage changes in supplier information security practices | |
| 166 | A.5.23 | Information security for use of cloud services | Establish processes for acquiring, using, managing and terminating cloud services according to corporate information security requirements | |
| 167 | A.5.24 | Information security incident management planning and preparation | Plan and prepare for information security incident management with relevant processes, roles and responsibilities | |
| 168 | A.5.25 |
Assessment and decision on information security events |
Assess information security events and decide if they should be categorized as incidents | |
| 169 | A.5.26 | Response to information security incidents | Respond to information security incidents in accordance with the documented procedures | |
| 170 | A.5.27 | Learning from information security incidents | Use knowledge gained from information security incidents to strengthen and improve information security controls | |
| 171 | A.5.28 | Collection of evidence | Establish and apply procedures for the identification, collection, acquisition and preservation of evidence related to information security events | |
| 172 | A.5.29 | Information security during disruption | Plan how to maintain information security at an appropriate level during disruption | |
| 173 | A.5.30 | ICT readiness for business continuity | Plan, apply, maintain and test ICT readiness according to business continuity objectives and requirements | |
| 174 | A.5.31 | Legal, statutory, regulatory and contractual requirements | Identify, document and keep up-to-date revant legal, statutory, regulatory and contractual information security requirements | |
| 175 | A.5.32 | Intellectual property rights | Implement appropriate procedures to protect intellectual property rights | |
| 176 | A.5.33 | Protection of records | Protect against loss, destruction, falsification, unauthorized access and unauthorized release of operational records | |
| 177 | A.5.34 | Privacy and protection of personal identifiable information | Identify and comply with requirements regarding the preservation of privacy and protection of personal identifiable information according to applicable laws, regulations and contractual requirements | |
| 178 | A.5.35 | Independent review of information security | Review information security management, including people, processes and technology at planned intervals | |
| 179 | A.5.36 | Compliance with policies, rules and standards for information security | Regularly verify compliance with information security policies, company standards and rules | |
| 180 | A.5.37 | Documented operating procedures | Document and make available to personnel concerned the operating procedures for information processing facilities | |
|
A.6 People controls
|
||||
| 181 | A.6.1 | Screening | Carry out reference checks on job candidates before their integration into the company according to the business requirements, the classification of information and the risks identified, cf. sub-clause 7.2 | |
| 182 | A.6.2 | Terms and conditions of employment | Include personnel and company information security responsibilities in employment contracts | |
| 183 | A.6.3 | Information security awareness, education and training | Educate, teach and train staff and stakeholders in information security, including policy and procedure updates | |
| 184 | A.6.4 | Disciplinary process | Formalize and communicate the disciplinary process for those who have committed an information security policy violation | |
| 185 | A.6.5 | Responsibilities after termination or change of employment | Define, enforce and communicate information security responsibilities and obligations that remain in effect after employment ends or changes | |
| 186 | A.6.6 | Confidentiality or non-disclosure agreements | Identify, document, review and sign confidentiality (non-disclosure) agreements to protect sensitive information | |
| 187 | A.6.7 | Remote working | Put in place security measures relevant to remote working to protect information outside of company premises | |
| 188 | A.6.8 | Information security event reporting | Provide a mechanism to promptly report actual or suspected information security events | |
|
A.7 Physical controls
|
||||
| 189 | A.7.1 | Physical security perimeters | Define and use security perimeters to protect areas with sensitive information and assets | |
| 190 | A.7.2 | Physical entry | Protect access areas with appropriate access security measures and access points | |
| 191 | A.7.3 | Securing offices, rooms and facilities | Design and implement physical security measures for offices, rooms and facilities | |
| 192 | A.7.4 | Physical security monitoring | Continuously monitor the premises to prevent unauthorized physical access | |
| 193 | A.7.5 | Protecting against physical and environmental threats | Design and apply protection against physical and environmental threats (such as natural disasters), intentional or unintentional | |
| 194 | A.7.6 | Working in secure areas | Design and apply safety measures for working in secure areas | |
| 195 | A.7.7 | Clear desk and clear screen | Define and enforce clear desk and clear screen rules for information processing facilities | |
| 196 | A.7.8 | Equipment siting and protection | Choose and protect a secure location for the equipment | |
| 197 | A.7.9 | Security of assets off-premises | Protect off-site assets | |
| 198 | A.7.10 | Storage media | Manage storage media throughout their life cycle (acquisition, use, transportation, and disposal) according to classification and business requirements | |
| 199 | A.7.11 | Supporting utilities | Protect information processing facilities against power outages and other support service failures | |
| 200 | A.7.12 | Cabling security | Protect electrical cables against interception, interference or damage | |
| 201 | A.7.13 | Equipment maintenance | Maintain equipment properly to ensure availability, integrity and confidentiality of information | |
| 202 | A.7.14 | Secure disposal or re-use of equipment | Check storage hardware to ensure secure deletion of sensitive data or licensed software | |
|
A.8 Technological controls
|
||||
| 203 | A.8.1 | User end point devices | Protect information stored, processed or accessible via a user end point device | |
| 204 | A.8.2 | Privileged access rights | Limit and manage the allocation and use of privileged access rights | |
| 205 | A.8.3 | Information access restiction | Restrict access to information and other assets according to access control policy | |
| 206 | A.8.4 | Access to code source | Appropriately manage access to source code, development tools and software libraries | |
| 207 | A.8.5 | Secure authentication | Apply secure authentication technologies and procedures according to the restrictions of the access control policy, cf. A.8.3 | |
| 208 | A.8.6 | Capacity management | Monitor and adjust resource usage according to scaling needs, cf. Capacity management plan, sub-clause 7.5.1 | |
| 209 | A.8.7 | Protection against malware | Apply protection against malware, raise staff awareness, cf. sub-clause 7.3 | |
| 210 | A.8.8 | Management of technical vulnerabilities | Obtain information on technical vulnerabilities of information systems, evaluate the company's exposure to these vulnerabilities and take appropriate measures | |
| 211 | A.8.9 | Configuration management | Define, document, enforce, monitor and review security, hardware, software and network configuration | |
| 212 | A.8.10 | Information deletion | Delete information, which is no longer necessary, on information systems, devices and other storage media | |
| 213 | A.8.11 | Data masking | Mask data according to access control policy, cf. A.8.3 respecting business requirements and applicable legislation | |
| 214 | A.8.12 | Data leakage prevention | Apply data leakage prevention measures of sensitive information to systems, networks and other devices | |
| 215 | A.8.13 | Information backup | Retain and regularly test backup copies of information, software and systems according to the topic-specific backup policy | |
| 216 | A.8.14 | Redundancy of information processing facilities | Apply information processing facilities with redundancy to meet availability requirements | |
| 217 | A.8.15 | Logging | Generate, maintain, protect and analyze logs of activities, exceptions, faults and other relevant events | |
| 218 | A.8.16 | Monitoring activities | Monitor networks, systems and applications and take appropriate action, cf. sub-clause 9.1 | |
| 219 | A.8.17 | Clock synchronization | Synchronize information processing system clocks to approved time sources | |
| 220 | A.8.18 | Use of privileged utilities programs | Restrict and tightly control the use of utility programs with the ability to override system and application security measures | |
| 221 | A.8.19 | Installation of software on operating systems | Apply procedures and measures to securely manage the installation of operational software | |
| 222 | A.8.20 | Networks security | Secure, manage and control networks and network devices to protect system and application information | |
| 223 | A.8.21 | Security of network services | Identify, apply and monitor security mechanisms, service levels and network service requirements | |
| 224 | A.8.22 | Segregation of networks | Segregate information services, users and information systems groups | |
| 225 | A.8.23 | Web filtering | Control access to external websites to reduce exposure to malicious content | |
| 226 | A.8.24 | Use of cryptography | Define and apply cryptography rules, including cryptographic keys | |
| 227 | A.8.25 | Secure development life cycle | Define and apply rules for the secure development of software and systems | |
| 228 | A.8.26 | Application security requirements | Identify, specify and approve information security requirements when developing or acquiring applications | |
| 229 | A.8.27 | Secure system architecture and engineering principles | Establish, document, maintain and apply secure systems engineering principles during the development of information systems | |
| 230 | A.8.28 | Secure coding | Apply secure coding principles to software development | |
| 231 | A.8.29 | Security testing in development and acceptance | Define and apply security testing processes during the development life cycle | |
| 232 | A.8.30 | Outsourced development | Direct, monitor and review activities relating to the development of outsourced systems | |
| 233 | A.8.31 | Separation of development, test and production environments | Separate and secure development, test and operational environments | |
| 234 | A.8.32 | Change management | Submit changes to information processing resources and information systems to change management procedures, cf. sub-clause 6.3 | |
| 235 | A.8.33 | Test information | Select, protect and manage test information appropriately | |
| 236 | A.8.34 | Protection of information systems during audit testing | Plan and agree between the tester and the appropriate level of management audit testing and other assurance activities involving the evaluation of operational systems | |
|
|
|
|
||




